American hyperscalers have launched European sovereign cloud offerings with dedicated data centers, EU-resident staff, and promises that customer data stays within European borders. Marketing materials emphasize physical separation, operational independence, and alignment with European requirements.
The technical architecture is real. The sovereignty claims require closer examination.
The question we should all be asking
Government agencies evaluating these offerings should start with two questions: Can this vendor access our data without our permission? Can foreign governments compel them to?
For infrastructure truly under European control, the answer to both questions is definitively no. For most offerings marketed as sovereign cloud, the answer is more complicated.
Under the CLOUD Act, location is irrelevant. Jurisdiction follows ownership. Even if data is hosted in Frankfurt or Paris, if it’s managed by a U.S.-based provider, it can legally be accessed by U.S. authorities. The US CLOUD Act of 2018 allows American authorities to compel US-based technology companies to provide requested data, regardless of where that data is stored globally.
Physical separation doesn’t change legal jurisdiction. While AWS claims there have been no access requests for data stored in the EU since 2020, this does not mean such requests cannot still come. While there is no automatic or unlimited access, on the basis of strict legal standards, it certainly can occur.
What sovereignty actually means
The European Commission published a Cloud Sovereignty Framework defining eight specific objectives with measurable criteria. The framework evaluates existence of legal, contractual, or technical channels through which non-EU authorities could compel access to data or systems.
Sovereignty means control over who can access data, under what circumstances, and subject to which legal framework. Marketing claims about EU data centers operated by EU staff don’t address whether the parent company can be compelled by foreign authorities to hand over access.
As long as a communications service provider is headquartered in the U.S., technical improvements and EU data residency do not change the fact that the CLOUD Act still applies. The jurisdictional problem remains regardless of where servers sit or who operates them day to day.
The Dutch example
The Netherlands demonstrates how procurement decisions based on sovereignty claims can backfire. Dutch public bodies had specifically chosen Solvinity to reduce their dependence on American firms and mitigate CLOUD Act risks. The acquisition of Solvinity by a US-based entity placed these systems squarely within the potential reach of US authorities.
Solvinity managed critical national infrastructure including the Netherlands’ citizen authentication system and government service portal. The acquisition exposed a structural flaw: deliberate choices for local providers offer no guarantee of long-term sovereignty when those providers can be acquired by US entities.
Sovereignty washing
American hyperscalers have recognized the market demand for sovereignty and now aggressively market sovereign cloud solutions, typically by placing datacenters on European soil or partnering with local operators. Critics call this sovereignty washing.
The term fits. When vendors market European data centers while remaining subject to extraterritorial legal reach, they’re selling compliance theater rather than actual control. Claims about control without compromise need a serious reality check. If a foreign government can compel data access, sovereignty is instantly compromised.
Government procurement officials evaluating these offerings need to distinguish technical features from legal guarantees. EU-based infrastructure operated by EU residents sounds reassuring until you ask which laws the parent company must obey.
What survives legal scrutiny
Real sovereign cloud infrastructure means the entity controlling access operates under European jurisdiction exclusively. Swedish cloud provider Safespring scores 86.25% on the EU Cloud Sovereignty Framework with 100% Swedish company ownership, Swedish governance, no dependency on non-European capital, and all employees as European citizens living in EU/EEA.
That level of independence is what sovereignty requires. The parent company, the operational entity, and the infrastructure all sit under European legal jurisdiction. No foreign authority can compel access without going through European legal processes.
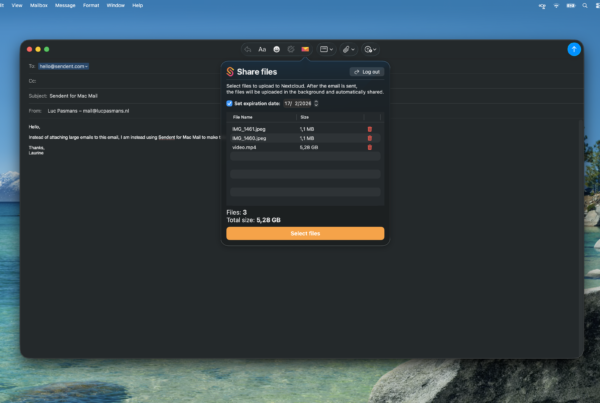
Platforms like Nextcloud offer similar guarantees when deployed on infrastructure you control or on providers genuinely independent from non-EU jurisdiction. The difference between marketing sovereignty and actual sovereignty comes down to who can legally compel access.
The bridge that works
Government agencies don’t need to abandon familiar collaboration tools to achieve sovereignty. Solutions that connect Microsoft interfaces to Nextcloud deployments on European infrastructure let organizations maintain workflow continuity while moving data under their actual control.
European alternatives like Nextcloud, OVHcloud, and Collabora offer genuine sovereignty. For many organizations, distinguishing real alternatives from false promises has become increasingly difficult.
The technical work of bridging tools to sovereign infrastructure is straightforward. What matters is ensuring the infrastructure itself survives the two basic questions: Can the vendor access your data without permission? Can foreign governments compel them?
If the answer to either question is anything other than a clear no, the sovereignty claims don’t survive legal scrutiny. Everything else is marketing.